-
 Purdue Secures NSF Grants to Lead Semiconductor Advancements
Purdue Secures NSF Grants to Lead Semiconductor AdvancementsPurdue University researchers have received over $5 million from the National Science Foundation and partners including Intel and Samsung. The funding, part of the NSF FuSe2 program, supports projects to enhance semiconductor performance, aligning with…
-
 Enhanced Cyber-Physical System Response with RL-RID-GridResponder
Enhanced Cyber-Physical System Response with RL-RID-GridResponderA new reinforcement learning-based engine, RL-RID-GridResponder, has been introduced to improve the resilience of cyber-physical power systems. By integrating role and interaction discovery (RID) to reduce action and state spaces, this approach provides…
-
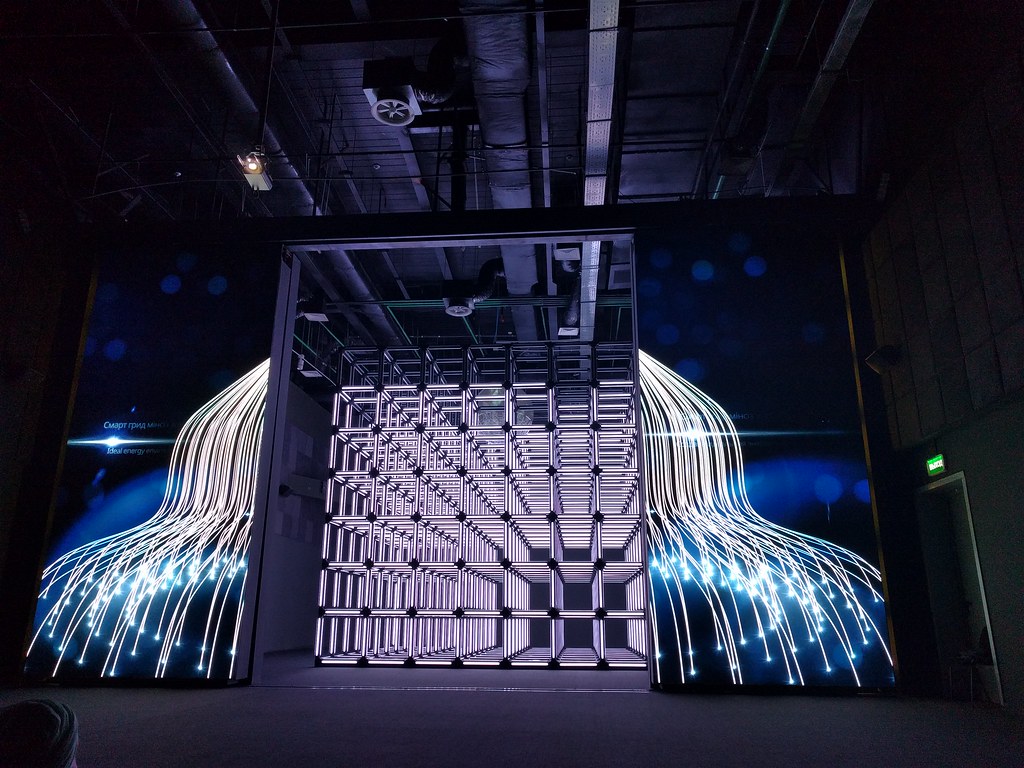 New Co-Simulation Environment Aims to Boost Resilience in Smart Grids
New Co-Simulation Environment Aims to Boost Resilience in Smart GridsResearchers have developed a co-simulation platform that integrates power grid and communication network simulations to improve cybersecurity in distribution grids. This modular setup allows testing of resilient operational management approaches under…
-
 Decentralized Autonomy in Building Cyber-Physical Systems
Decentralized Autonomy in Building Cyber-Physical SystemsA new framework introduces decentralized autonomous systems for building management, combining Decentralized Autonomous Organizations (DAOs), digital twins, and large language models (LLMs) to enhance building self-management and transparency. Unlike…
-
 UAH Secures $300K NSF Grant to Strengthen Cyber Defense in Intelligent Systems
UAH Secures $300K NSF Grant to Strengthen Cyber Defense in Intelligent SystemsResearchers at the University of Alabama in Huntsville (UAH) and the University of South Carolina are both focused on bolstering security in intelligent cyber-physical systems (iCPS). Supported by $300,000 NSF grants, UAH’s Avimanyu Sahoo and USC’s…
-
 UVA Engineering’s Jack Stankovic Receives IEEE Medal
UVA Engineering’s Jack Stankovic Receives IEEE MedalUniversity of Virginia Professor Emeritus Jack Stankovic received the IEEE's 2024 Simon Ramo Medal for his pioneering work in computer science fields like real-time systems, distributed processing, and cyber-physical systems. Stankovic's influential…
-
 CS team receives NSF grant to Improve perception for small robots and drones
CS team receives NSF grant to Improve perception for small robots and dronesThe University of Illinois Urbana-Champaign team, funded by a $1.2 million NSF grant, is pioneering the use of millimeter wave radar to enhance small robots' and drones' perception in challenging environments. By combining radar with machine learning,…
-
 Call for Papers - SLE 2025
Call for Papers - SLE 2025We are pleased to invite you to submit papers to the 18th ACM SIGPLAN International Conference on Software Language Engineering (SLE) which is devoted to the principles of software languages: their design, their implementation, and their evolution. The…
-
 Call for Papers ENASE 2025
Call for Papers ENASE 2025The mission of ENASE (Evaluation of Novel Approaches to Software Engineering) is to be a prime international forum to discuss and publish research findings and IT industry experiences with relation to novel approaches to software engineering.
-
 PhD Positions Available – Cyber-Physical Systems Research
PhD Positions Available – Cyber-Physical Systems ResearchThe University of Malaga, in collaboration with Prof. Ricardo Sanfelice (University of California, Santa Cruz, and Director of the Cyber-Physical Systems Research Center), invites applications for two pre-doctoral contracts funded by the Malaga…
-
 Postdoctoral Position at GEODES, Software Engineering Group, Université de Montréal
Postdoctoral Position at GEODES, Software Engineering Group, Université de MontréalThe GEODES Software Engineering Group at Université de Montréal is seeking a postdoctoral researcher for a cutting-edge project that leverages digital twins and artificial intelligence to accelerate discoveries in the field of advanced materials.Project…
-
 CfP: 31st IEEE Real-Time and Embedded Technology and Applications Symposium (RTAS 2025)
CfP: 31st IEEE Real-Time and Embedded Technology and Applications Symposium (RTAS 2025)RTAS is a top-tier conference with a focus on systems with timing requirements. RTAS’25 welcomes papers describing applications, case studies, methodologies, tools, algorithms or operating systems, middleware or hardware innovations that contribute to…
-
 CfP: 16th ACM/IEEE International Conference on Cyber-Physical Systems (ICCPS 2025)
CfP: 16th ACM/IEEE International Conference on Cyber-Physical Systems (ICCPS 2025)CM/IEEE International Conference on Cyber-Physical Systems (ICCPS) is the premier forum for presenting and discussing the most significant recent technical research contributions in the field of Cyber-Physical Systems (CPS). ICCPS 2025 will be part of…
-
 Position Opening: Chair, Department of Electrical and Computer Engineering, Vanderbilt University
Position Opening: Chair, Department of Electrical and Computer Engineering, Vanderbilt UniversityThe Vanderbilt University School of Engineering is seeking nominations and applications for the Chair of the Department of Electrical and Computer Engineering (ECE). This position calls for a visionary leader to enhance the department's global standing…
-
 CfP: SEAMS 2025
CfP: SEAMS 2025We are implementing a two-round submission process for the Research Track, with deadlines in October 2024 and December 2024. This approach will provide authors with an opportunity to submit a revised version of their paper in the second round. Accepted…
-
 CfP: The 40th ACM/SIGAPP Symposium on Applied Computing (SAC 2025) Cyber-Physical Systems Track
CfP: The 40th ACM/SIGAPP Symposium on Applied Computing (SAC 2025) Cyber-Physical Systems TrackThe vision of CPS faces some core challenges of multidisciplinary research, as their relevant technologies appear in diverse areas of science and engineering. Therefore, there is an emerging consensus that new methodologies and tools are urgently needed…
News