-
 New AI Framework Optimizes Electric Taxi Charging Under Solar Power Uncertainty
New AI Framework Optimizes Electric Taxi Charging Under Solar Power UncertaintyAs cities increasingly adopt electric vehicles (EVs) for public transportation, a new study proposes a smart solution to one of the sector’s biggest challenges: managing unpredictable solar energy while ensuring efficient service. Researchers have…
-
 Predictive AI Model Could Help Forecast Neurodegenerative Diseases
Predictive AI Model Could Help Forecast Neurodegenerative DiseasesA team of researchers at USC, led by Paul Bogdan, has developed an AI-based predictive model to forecast brain aging and detect early signs of neurodegenerative diseases like Alzheimer’s. Supported by multiple NSF grants, this innovative system combines…
-
 New Tool Portal: Automated Rapid Certification Of Software (ARCOS)
New Tool Portal: Automated Rapid Certification Of Software (ARCOS)We're excited to announce the launch of the Automated Rapid Certification Of Software (ARCOS) Tool Portal — a new DARPA-supported virtual resource for the research and development and certification communities.The ARCOS Tool Portal provides open access…
-
 Innovative Research Enhances Robustness Evaluation in Medical AI Systems
Innovative Research Enhances Robustness Evaluation in Medical AI SystemsA groundbreaking study titled "Evaluating Robustness of Learning-Enabled Medical Cyber-Physical Systems with Naturally Adversarial Datasets" has been recognized for its significant contribution to the field of medical AI. Authored by Sydney Pugh (…
-
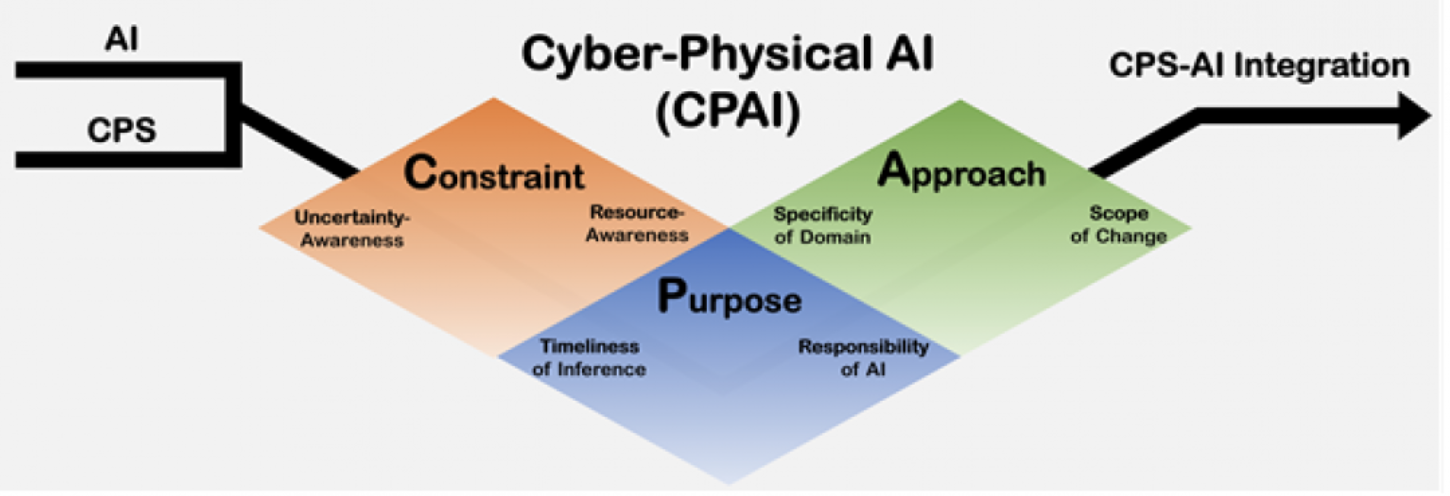 DGIST Introduces World’s First Concept of "Cyber-Physical AI" (CPAI)
DGIST Introduces World’s First Concept of "Cyber-Physical AI" (CPAI)A research team led by Professor Kyung-joon Park at DGIST has proposed the world’s first systematic concept of Cyber-Physical AI (CPAI)—a new framework for integrating artificial intelligence (AI) with Cyber-Physical Systems (CPS). This pioneering…
-
 Xu Receives Bement Award for Groundbreaking Cybersecurity Research
Xu Receives Bement Award for Groundbreaking Cybersecurity ResearchDongyan Xu, Samuel D. Conte Professor of Computer Science at Purdue University and director of CERIAS, has been awarded the 2024 Arden L. Bement Jr. Award — Purdue’s highest honor for contributions to pure and applied science and engineering. Xu is…
-
 Bridging the Gap: New Research Framework Unites AI and Cyber-Physical Systems
Bridging the Gap: New Research Framework Unites AI and Cyber-Physical SystemsDate: April 17, 2025Byline: Science of Security NewswireIn a significant stride toward integrating Artificial Intelligence (AI) with Cyber-Physical Systems (CPS), researchers have introduced a comprehensive framework aimed at harmonizing these two…
-
 Mizzou Engineering Research Highlights Security and Privacy Risks of AI in Extended Reality (XR)
Mizzou Engineering Research Highlights Security and Privacy Risks of AI in Extended Reality (XR)At the University of Missouri (Mizzou) College of Engineering, researchers are tackling the growing cybersecurity and privacy challenges arising from the fusion of artificial intelligence (AI) and extended reality (XR) — immersive technologies combining…
-
 UTRGV Expands AI Research and Education with $2.8M NSF Grant
UTRGV Expands AI Research and Education with $2.8M NSF GrantThe University of Texas Rio Grande Valley (UTRGV) has secured a $2.8 million grant from the National Science Foundation’s ExpandAI Program to advance its research and education efforts in artificial intelligence. The project, titled AI Research and…
-
 CPS-IoT Week 2025 (Student Travel Awards) Early-Bird Registration Extended to April 14
CPS-IoT Week 2025 (Student Travel Awards) Early-Bird Registration Extended to April 14On behalf of the CPS-IoT Week organizing committee, we are delighted to announce the availability of student travel awards, thanks to the generous support from NSF and ACM SIGBED. Eligibility information, important dates, and instructions to apply can be…
-
 AI-Driven Speed Control System Marks One Year of Safer Roads on I-24
AI-Driven Speed Control System Marks One Year of Safer Roads on I-24One year ago, the Vanderbilt Vector Lab and the Institute for Software Integrated Systems at Vanderbilt University launched an AI-driven Variable Speed Limit (VSL) control system along a 17-mile stretch of Interstate 24 in Middle Tennessee. Powered by…
-
 Call for Participation: IEEE PerCom 2025, March 17-21, Washington D.C.
Call for Participation: IEEE PerCom 2025, March 17-21, Washington D.C.======================================================================== CALL FOR PARTICIPATION ======================================================================== IEEE PerCom 2025The Twenty Third IEEE International Conference…
-
 DESTION 2025 Call For Papers extended deadline approaching (March 6th)!
DESTION 2025 Call For Papers extended deadline approaching (March 6th)!About DESTIONDESTION provides a premier forum for researchers and engineers from academia, industry, and government to present and discuss challenges, promising solutions, and applications in design automation for CPS and IoT. DESTION 2025 has a broad…
-
 Vanderbilt Engineers Pioneer AI-Powered Traffic Safety with Smart Highway Research
Vanderbilt Engineers Pioneer AI-Powered Traffic Safety with Smart Highway ResearchVanderbilt professors Jonathan Sprinkle and Dan Work have teamed up to enhance highway safety and efficiency using AI-powered autonomous vehicle technology. Their groundbreaking research, supported by the National Science Foundation and key industry…
-
 David Hyde Awarded NSF CAREER Grant to Advance Cloud Computing, AI, and Quantum Research
David Hyde Awarded NSF CAREER Grant to Advance Cloud Computing, AI, and Quantum ResearchDavid Hyde, an assistant professor of computer science at Vanderbilt University, has been awarded a prestigious National Science Foundation (NSF) CAREER Award. This award, totaling $547,484, supports early career faculty with the potential to lead…
-
 UAH assistant professor Dr. Avimanyu Sahoo recognized as part of 4th Annual Engineering Showcase (Engineers Week 2025)
UAH assistant professor Dr. Avimanyu Sahoo recognized as part of 4th Annual Engineering Showcase (Engineers Week 2025)UAH has been awarded an NSF grant that aims to characterize the vulnerabilities of learning-based intelligent cyber-physical systems (CPS) and develop defenses against potential threats.
News