Classification of UDP Traffic for DDoS Detection
ABSTRACT
1 Introduction
UDP traffic has recently been used extensively in flooding- based distributed denial of service (DDoS) attacks, most no- tably by those allegedly launched by the Anonymous group against various government and commercial websites (e.g., FBI, Universal Music Group, etc.). Despite extensive past research in the general area of DDoS detection/prevention, the industry still lacks effective tools to deal with DDoS at- tacks leveraging UDP traffic. This work presents our preliminary investigation into the proportional-packet rate as- sumption which has been proposed by past research [2], and the use of this criterion to classify UDP traffic with the goal of detecting malicious addresses that launch flooding-based UDP DDoS attacks. We examined various datasets to verify whether the assumption holds for UDP traffic, through extensive empirical analysis of UDP traffic from a large number of production networks as well as traffic generated by popular attack tools (e.g., LOIC, Stacheldraht, Trin00). Our find- ings [1] indicate that the proportional-packet rate assumption largely holds for UDP traffic and can be used to create an effective classifier for detecting flooding-based UDP DDoS attacks.
2 Approaches
Our approach is based on the assumption that under normal operations, the packet rate in one direction is proportional to the packet rate in the opposite direction [2]. While UDP does not provide delivery confirmation, a benign UDP-based application usually implements some acknowledgment mechanism to ensure the other party is still alive and/or received the sent packets.
2.1 Basic Approach
Our basic classification algorithm works as follows. For every source IP address that sends UDP packets to a monitored destination IP address (or subnet), we calculate a ratio function within a preset time window, and use the value to differentiate benign and DDoS sources.
Let α(src addr) be the number of packets sent from src addr to the monitored address and β(src addr) be the number of packets sent to src addr from the monitored address.
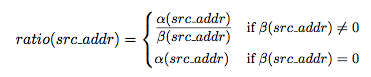
The intuition is that under normal operations, the number of packets sent from the source to the monitored target will be proportional to the number of packets sent from the target to the source, due to the proportional-packet rate assumption. Thus for benign traffic the ratio function is expected to be below some maximum threshold. If a source IP address is launching a flooding attack against the target, the number of packets sent from the source will far exceed the number of packets sent to it by the target; thus the ratio function will be higher than that of a benign one. The β(src addr) = 0 case captures the benign one-way communication pattern. In such cases the ratio function is equal to the packet rate sent from the source to the monitored target. In those benign ap- plications the packet rate will be as well much lower than that from a flooding attack source. Our classifier requires little resources to deploy, and could operate in either port-mirrored mode or inline mode, as long as traffic in both directions can be monitored.
2.2 Interaction with Source
A still-under-development version of our classifier can also directly interact with a suspicious source. For instance, a benign application may opt to use non-acknowledgement packets (similar to the TCP NACK packets) instead of acknowledgement packets for delivery confirmation. In this case, when the ratio value exceeds the pre-set threshold an IPS can temporarily block the source and observe whether the mon- itored target sends back packets (presumably “NACK pack- ets”), in which case the blocked source will be released. This could potentially improve classification accuracy.
3 Experimentation
We conducted our experiments on data from a large number of production networks including large corporations (edge and core), ISPs, universities, financial institutions, etc. In addition, we also conducted experiments on the DETER testbed as well as a twenty-host testbed of our own. In our experiments we found that the vast majority of UDP-based applications follow this proportional-packet rate rule.1 However we did observe exceptions in some UDP-based applications: applications that adopt a short sender-receiver initial two-way communication, followed by a one-way burst of UDP packets (e.g., the Session Initiation Protocol - SIP and the T.38 protocol for fax) or applications that send a short one-way burst of packets (by protocol design no response message is necessary, e.g., Syslog over UDP or older versions of Netflow). All the experiments indicate that proportional-packet rate assumption generally holds for be- nign UDP traffic and can be used as a reasonable criterion to differentiate DDoS and non-DDoS UDP traffic. Moreover, our classifier was able to detect a previously unknown UDP DDoS attack which was subsequently verified by manual analysis. Detailed experimentation set up and results will be shown in the poster.
References
-
[1] A. G. Bardas, L. Zomlot, et al. Classification of UDP traffic for DDoS detec- tion. In 5th USENIX Workshop on Large-Scale Exploits and Emergent Threats (LEET), 2012.
-
[2] T. M. Gil and M. Poletto. MULTOPS: a data-structure for bandwidth attack detection. In Proceedings of 10th Usenix Security Symposium, 2001.
1Note that packet rate is different from data rate. When measuring packet rates we only count the number of packets sent per time unit; the sizes of these packets do not affect the metric.
Award ID: 1018703